Hey! It’s been awhile since the last AppSec Travels blog. In this post we wanted to write about a vulnerability that is near and dear to our hearts: User Enumeration. In the world of application security, some vulnerabilities are loud and catastrophic, while others are subtle, acting as silent facilitators for more significant attacks. User […]
Appsec
Thoughts on the new OWASP Top Ten
The 2025 OWASP Top 10 is here, and it might be my gray hair speaking, but it seems everything old is new again. For old hats–like myself, who relied on the initial 2003 list to guide my early penetration testing career (thank you, Classic ASP, for the good times)–the 2025 list has less shocking revelations […]
SDLC – Managing risk in Software through the compounding effect of control gates
By Cameron White If you’ve ever watched someone run the hurdles in a track meet, you may share my amazement at their agility to consistently leap each hurdle at speed when the pressure to perform is on. The compounding exertion to clear each barrier is not hard to imagine, and when you’re trying it yourself, […]
How AI and LLMs Will Shape AppSec in 2025
Four Predictions for AppSec in 2025 By Ken Johnson and Seth Law In this joint blog from Seth Law at Redpoint and Ken Johnson at DryRun Security, we highlight how 2025 will be a pivotal year for large language models (LLMs) in AppSec. Building on the momentum of 2024, LLMs are moving from novelty to […]
The experience of a beginner in the field of Appsec.
My name is Trevon Greenwood, and I am a Junior Security Analyst at Redpoint Security. This post outlines my experience as a beginner in the field and what a day at work looks like for me. I have been with Redpoint for just over a year now, so I think I’ve accrued enough experience as […]
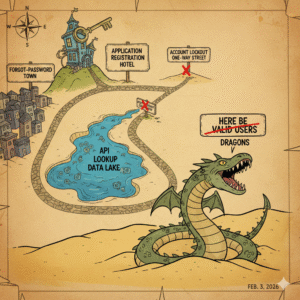
AppSec Travels 3: Account Takeover
During a recent assessment, our team came upon a vulnerability that felt like finding a hidden door in a seemingly secure fortress. The discovery involved the password-reset mechanism of an application, allowing us to reset any user’s password with just their email address. This flaw circumvents authentication, giving unauthorized access to user accounts. Here’s how […]
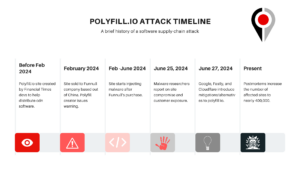
Polyfill io and Surveyor’s Continuous Dependency Monitor
In the aftermath of the polyfill supply-chain attack that reportedly compromised the security of some 100,000 applications across the Internet last week (arstechnica reports that over 384K sites are still pulling the package subsequently), our team at Redpoint realized quickly that it was a real-world case of feature within Redpoint’s Surveyor tool. That is, lead […]
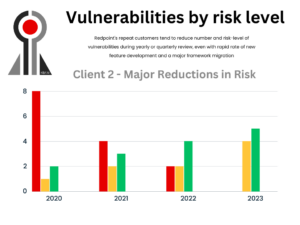
A Redpoint Customer Security Journey
In Redpoint Security’s existence as an application security firm, we have seen a range of clientele who manifest a whole host of differences: development teams and applications that range remarkably small and large, different levels of security maturity, compliance requirements that are relatively lax as opposed to highly demanding with a rapidly rushing SLA (Service-Level […]