By Cameron White If you’ve ever watched someone run the hurdles in a track meet, you may share my amazement at their agility to consistently leap each hurdle at speed when the pressure to perform is on. The compounding exertion to clear each barrier is not hard to imagine, and when you’re trying it yourself, […]
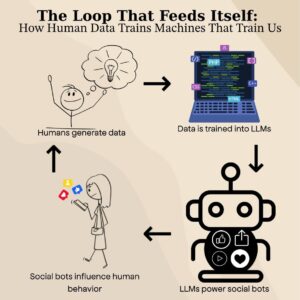
The Loop that Feeds Itself: How human data trains machines that train us
A decadent introduction by Jade Lee Our world is made up of an astronomical amount of data. Beyond internet traffic and hard drives, we now supply a consistent stream of data through our cars, refrigerators, doorbells, and most importantly, our words. Almost the entire expanse of human thought and home can be translated into vector embeddings, […]
How AI and LLMs Will Shape AppSec in 2025
Four Predictions for AppSec in 2025 By Ken Johnson and Seth Law In this joint blog from Seth Law at Redpoint and Ken Johnson at DryRun Security, we highlight how 2025 will be a pivotal year for large language models (LLMs) in AppSec. Building on the momentum of 2024, LLMs are moving from novelty to […]
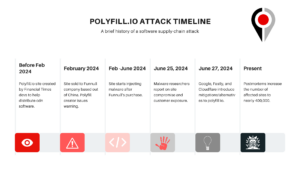
Polyfill io and Surveyor’s Continuous Dependency Monitor
In the aftermath of the polyfill supply-chain attack that reportedly compromised the security of some 100,000 applications across the Internet last week (arstechnica reports that over 384K sites are still pulling the package subsequently), our team at Redpoint realized quickly that it was a real-world case of feature within Redpoint’s Surveyor tool. That is, lead […]
AppSec Travels Part 2: Access-Control Bypass
What happens when combined technologies counteract security controls? This is another in Redpoint’s blog series AppSec Travels where we walk you through interesting findings we’ve discovered in vulnerability assessments. AppSec Travels is on ongoing series without a regular cadence because frankly some assessments are perfunctory security checks lacking in exciting findings and we sort of […]
AppSec Travels Part I: Function Overload
Token Caching This is our first blog of AppSec Travels where we walk you through interesting findings we’ve discovered in vulnerability assessments. This will be on ongoing series without a regular cadence because frankly some assessments are perfunctory security checks lacking in exciting findings and we sort of doubt anyone wants to read findings write-ups […]
Redpoint Services
Application Security in 2024: A Look at Redpoint’s Service Offerings In today’s rapidly changing landscape of information security, protecting your applications is crucial. The statistics speak for themselves: data breaches can incur significant costs, with an average cost of $4 million per breach, according to IBM. It’s clear that the threat of exploitation is widely […]
Redpoint and Code
Why code security by coders? The secret to comprehensive security is knowing how an attacker thinks and how a developer creates. The important thing to remember for finding and helping remedy security flaws, is that it requires assessments where our testers/researchers can toggle between two frames of mind. First, We look at your application like […]