Application Security Fundamentals (APPSEC-101)
Building modern applications requires an understanding of security exploits, vulnerabilities, tools and techniques. This course provides students with knowledge of these common vulnerabilities, open source tools and professional techniques used to build secure software. Students will be introduced to open-source tools and taught how these tools can complement the development process. Most importantly, this course will teach students how to identify flaws in code and running applications, as well as approaches used to fix these flaws. This training will review items from the latest iteration of OWASP’s Top 10 Web Application Security Risks (https://owasp.org/www-project-top-ten/) and cover the tools and techniques for identifying and preventing those vulnerabilities in code.
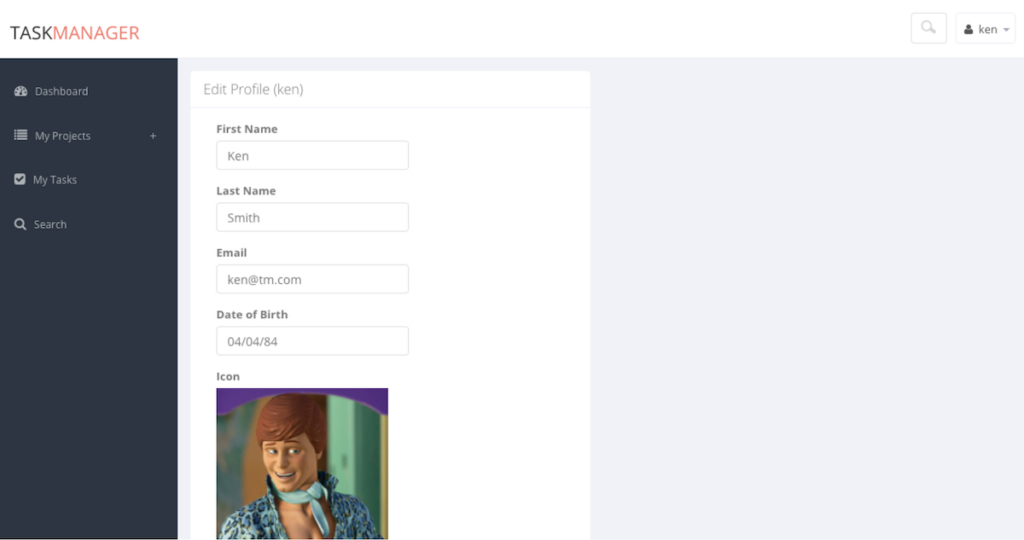
For the course, Redpoint team members have developed a custom-made vulnerable application: Vulnerable Task Manager, or VTM: the repo is here (feel free to play around with the application and find its vulnerabilities).
AppSec 101 students practice exploitation techniques against VTM and learn basic security principles and OWASP Top Ten vulnerability classes in the course of the training. We provide additional training with web application security once your team has mastered APPSEC-101, with our more advanced companion course APPSEC-102. To find out more and to see if these trainings could be right for your team, reach out to us at info@redpointsecurity.com.
Practical-Secure Code Review (SCR-301)
The Practical Secure Code Review training course is designed to teach developers and security professionals a repeatable process for reviewing source code for security flaws. It addresses multiple common challenges in modern secure code review, including overcoming common obstacles to efficient secure code-review time use as well as learning how to distill the source code of an application quickly to understand its functional and security aspects, whether you’re examining an entire code base, a pull request, or a new feature. This course is intended for advanced developers with several years of experience working with application development and some experience with security engineering and troubleshooting problems in code.
Students will be able to build personal secure code review techniques by learning a proven methodology to perform security analysis of any source code repository and identify security flaws, no matter the size of the code base, or the framework, or the language. Redpoint’s founder helped develop the time-proven practical secure-code review methodology based on years of secure code-review experience. The course includes hands-on demonstrations of the methodology as well as a workshop that directs students to use the methodology with their own selected code-base.
The course has been presented with students across five continents and at major industry conferences (DEFCON, Blackhat) and with major corporations in North America, Europe, Asia, and Oceania. The course overview is attached below for more information, but don’t hesitate to reach out to us for more information.
Mobile Security 101-a and 101-i
Modern mobile iOS and Android applications have their own unique security exploits, vulnerabilities, tools, and techniques. These courses provide students with knowledge of common vulnerabilities, open-source tools and professional techniques used to exploit mobile apps, and the counter-development techniques for building and testing secure software. Students will be introduced to open-source tools and taught how these tools can complement the development process. Most importantly, this course will teach students how to identify flaws in code and running applications, as well as approaches used to fix these flaws. This training will review items from OWASP’s Mobile Application Security Verification Standard (https://mobile-security.gitbook.io/masvs/) and the last version of the OWASP Mobile Top Ten (https://owasp.org/www-project-mobile-top-10/), covering the tools and techniques for identifying and preventing those vulnerabilities in code.
Threat Modeling 101 (TM 101)
Becoming adept at developing threat models for the range of assets and processes that support an organization that develops modern applications requires an understanding of security layers, threat types, the infrastructure that supports applications and development processes, threat actors who array against the secure operation and development of software and customers and their data, as well as understanding the changing threat landscape filled with potential zero-day exploits, new insiders who intentionally or not could elevate application risks. This course provides students with knowledge of these common threat modeling methodologies, perspectives on different viewpoints from which to approach a threat model, strategies for identifying and engaging key organizational stakeholders who can help make threat models more useful and accurate.
Students will come away from the course with an understanding of how to implement a threat model within the SDLC (software development lifecycle) through steps of information gathering, threat identification, mitigation identification, output and communication in the form of gap analysis, threat matrices, and finding enumeration. In addition, students will learn common Threat Modeling methodologies (STRIDE, PASTA, DREAD), understand threat modeling in different perspectives: asset-focused, process-focused, threat actor-focused, or attack type-focused.