Automated tools can only go so far in detecting complex security issues. Our seasoned security professionals conduct meticulous manual source code reviews using some automated tools to help focus the review, diving deep into the source code to find intricate vulnerabilities that automated code scans miss. With a keen eye for detail and extensive experience in information security, we tease out the code with the most important security implications for your application and then scrutinize it for potential risks. Code-level remediation advice follows, which provides developers with solutions in perhaps their most useful form.
To understand Redpoint Security’s process for conducting manual source code reviews, it’s worth emphasizing that our founder, Seth Law, in concert with Ken Johnson, developed The Absolute AppSec methodology for Secure Code Review, one of the most popular frameworks for conducting secure code review for modern applications. The methodology Seth and Ken developed focuses on helping AppSec testers conducting code reviews to have a set of principles and frameworks for approaching a new codebase, orienting themselves in the code regardless of level of familiarity regarding the languages and technologies involved, and developing a gameplay for analyzing the codebase for bugs.
The first incarnation of the Absolute AppSec secure-code review methodology and the course Seth and Ken taught about the approach used Bill & Ted’s excellent adventure as an extended motif for getting good at code review. From that auspicious beginning, they developed the methodology as well as the Circle-K framework for ensuring that code reviews build out enhanced review checklists derived from the specific knowledge gained from poring over the application codebase.
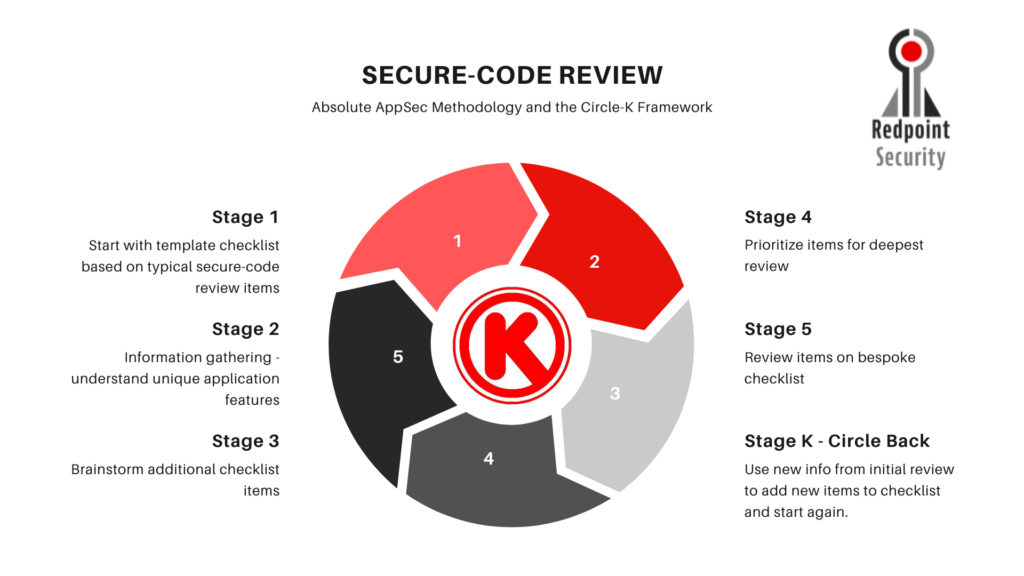
This Absolute AppSec methodology for Secure Code Review and its Circle-K framework informs how Redpoint Security approaches Secure Code Review engagements. Testers have a repeatable step-by-step guide to performing reviews and a feedback loop that makes the review smarter as the testers learn more about your codebase and application. As a result of our Secure Code Review process, the experience Redpoint testers bring to code review projects is second to none. We use this expertise to provide you, and your developer team reports full of actionable remediation advice where we point to specific lines of code for fixes. There’s a reason why we say we do code security by coders.
If you’re curious to learn more about how a Redpoint Security manual source code review could help your application improve and how you can better protect your assets and customers’ data, please complete the form below.